The Most Used Security Technologies With Their Net Cost Saving That They Provide, 2019
Cybersecurity | Global
All organizations could benefit from the reduction in cybercrime cost enabled by further investment in advanced identity and access management. Security intelligence and threat sharing is widely deployed by companies and provides the greatest cost savings when compared with the levels of spend. It is not only an important enabling technology for both discovery and investigation activities, but also it is an important source of information to understand threats and better target resources against anticipated attacks. Security should to be a core competency across the organization and embedded in all that a business is and does. From people to data to technologies, every aspect of business invites risk. Despite their investments, business leaders still need to improve the economic value of their cybersecurity strategies.
Take a glance at the most used security technologies and the total cost saving provided 2019:
- Security intelligence and threat sharing are ranked as the most used security technology with a rate of 67%, with a total cost saving of US$ 2.26 million.
- Advanced identity and access management is ranked as the second most used security technology with a rate of 63%, provides a substantial net cost saving of US$1.83 million.
- Advanced perimeter controls come at next as a used security technology with a rate of 58%, with a net saving cost of US$ 0.16 million.
- Cryptography technologies also listed as a used security technology with a rate of 55%, with a net cost saving of US$ 0.85 million.
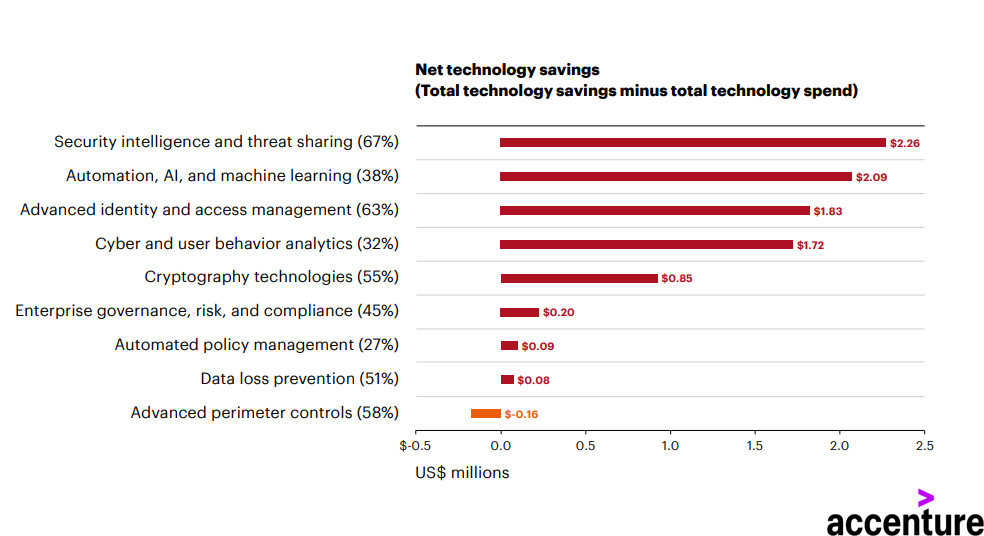
A Graph Shows The Most Used Security Technologies & Their Toal Savings, 2019.